
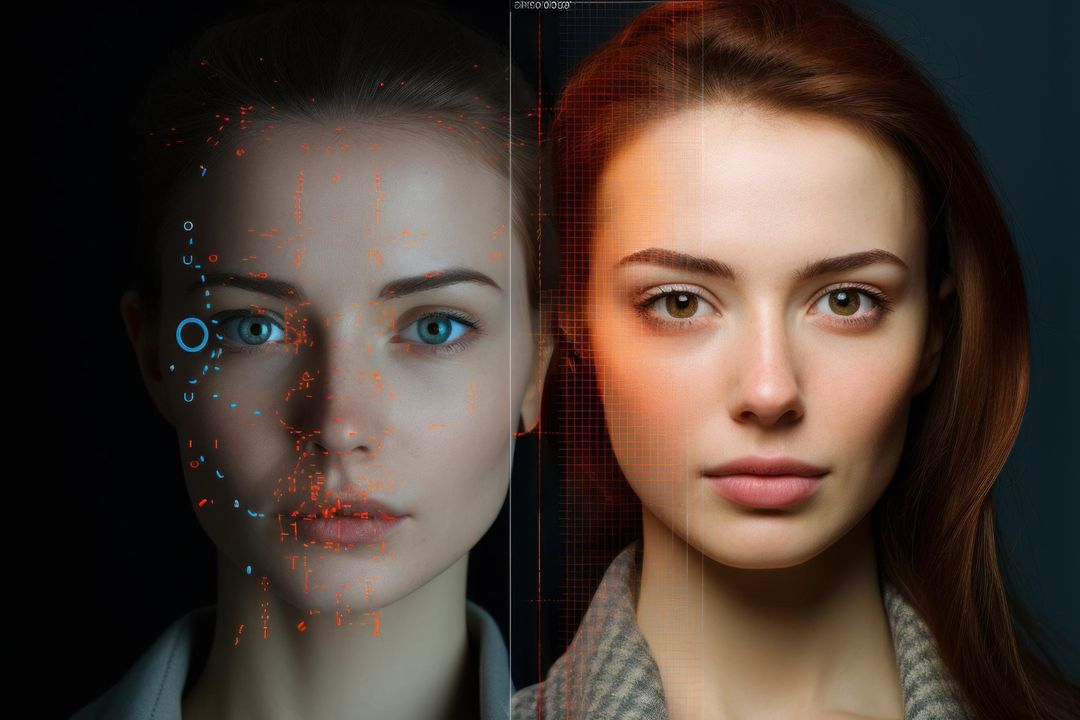
Verify identity and media across voice, video, image, and text powered by a hybrid multimodal forensic engine that determines what can be trusted and what to do next.




.png)







.png)
.png)




Verify and Secure Your Essential Channels
Integrate real-time deepfake defense directly into your current communication stack and apps.
Contact Center Security
Contact centers face sophisticated voice deepfakes that bypass traditional security and human detection. Blackwater Verify secures these channels with real-time detection, allowing agents to interact confidently and maintain efficiency while stopping fraudulent callers


Secure Video Conferencing
AI-driven deepfakes are increasingly used to impersonate executives during video conferences, causing massive financial losses. Blackwater Verify mitigates this threat by providing real-time detection, ensuring secure and confident communication across all major corporate platforms.
Access Security & Fraud Prevention
Financial institutions face rising deepfake threats that bypass traditional KYC checks. Blackwater Verify secures the onboarding process through real-time detection, enabling organizations to stop identity fraud and verify new customers with complete confidence.

Brand & Executive Proctection
Executives face reputation-damaging deepfakes and fraud. Blackwater Verify partners with intelligence experts to scan the web for unauthorized impersonations, providing real-time detection and alerts that proactively safeguard leaders' digital identities and professional standing.


Protecting Critical Communications Across Key Industries
From financial hubs to government sectors, Blackwater Verify secures critical infrastructure against the escalating threat of deepfake exploitation.

Recent Highlights
Shift the risk.
Secure your lead.
From hardening onboarding workflows to neutralizing synthetic fraud at the source, Blackwater Verify ensures your defenses evolve faster than the threats.








.png)

